In recent years, along with continuously evolving communication technology, the rapid growth of internet is playing an increasingly important role in boosting economic development, promoting social progress, transmitting advanced culture, enhancing interpersonal communication, and in many other aspects. However, at the same time, there are unscrupulous persons who take advantage of the internet to spread obscene pornography and other harmful information, and even gamble, commit fraud and other criminal activities, disseminate hate speech, sedition and rumors, and undermine social stability and national cohesion.
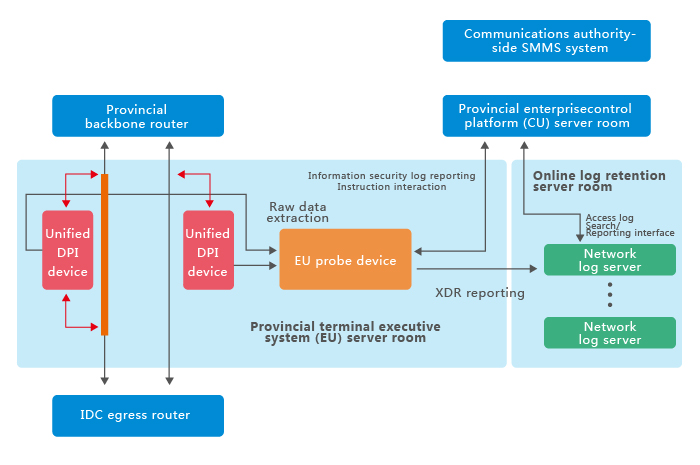
When we make full use of the internet’s positive features, the negative impact should be minimized to the lowest level, hence security audit and harmful information regulation of the internet must be taken up without delay. Especially, IDCs—the main information source of the internet—must adopt certain technology and management methods to guarantee IDC business to develop stably, healthily and rapidly.
To achieve the above targets, it is necessary to adopt advanced technical means, enabling real time monitoring of operation status of all websites and services of an IDC, timely discovery of illegal content in an IDC, implementation of real-time effective technical processing, and realize real-time, intelligent, completely automated security audit and information regulation of the IDC.

 CN
CN